Understanding Group Policy Objects (GPO) in Windows: A Complete Guide
Group Policy Objects (GPOs) are a powerful feature in Windows operating systems that allow system administrators to manage and control the settings of multiple computers and users in an Active Directory environment. They provide a centralized way to enforce security settings, configure user profiles, and manage system behaviors across an entire network. In this blog post, we will dive deep into what GPOs are, how they work, and the best practices for using them effectively in an enterprise environment.

What is a Group Policy Object (GPO)?
A Group Policy Object (GPO) is a collection of settings that define how systems and users behave within an Active Directory environment. GPOs are used to control a wide range of system configurations such as password policies, desktop settings, application restrictions, and network configurations. These policies are applied to specific users, groups, or computers in the network based on criteria set by system administrators.
GPOs work by modifying registry settings and applying them to machines or users within the scope of the policy. These changes can be applied either at the computer level (affecting all users on the machine) or at the user level (affecting individual users across different machines).
Types of Group Policy Objects
There are two main types of Group Policy Objects:
- Local GPO
- Domain-based GPO
Local GPO: A local GPO applies settings to a single machine and is not associated with any Active Directory domain. These are primarily used in non-networked environments or on individual computers.
Domain-based GPO: A domain-based GPO applies to all computers and users within an Active Directory domain. These GPOs are stored in the domain’s Group Policy container and can be applied to any number of machines or users within the domain, offering centralized management.
How Does GPO Work?
GPOs function through a process called Group Policy Processing, which occurs when a user logs in or a computer starts up. The system checks the policies applied to the user or computer and processes them accordingly. The processing order determines which policies take precedence in case of conflicts:
- Local Group Policy
- Site-level GPO
- Domain-level GPO
- Organizational Unit (OU)-level GPO
GPOs are processed in this order, with each level overwriting the settings applied by the previous one. For example, a GPO applied at the Organizational Unit (OU) level will take precedence over a GPO applied at the Domain level.
Key Components of a GPO
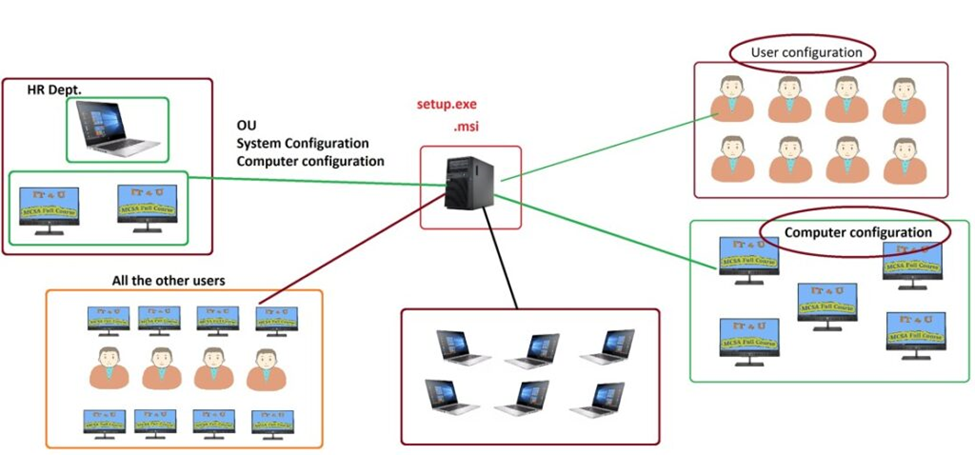
Each GPO consists of two primary components:
- Computer Configuration: These settings apply to computers regardless of which user is logged in. Examples include software installation, security settings, and system configurations.
- User Configuration: These settings apply to users regardless of which computer they log into. Examples include desktop settings, Internet Explorer settings, and user-specific security settings.
GPOs can be created and edited using the Group Policy Management Console (GPMC), which provides a user-friendly interface for managing these policies.
Creating and Managing GPOs
Creating and managing Group Policy Objects requires access to the Group Policy Management Console (GPMC), a tool available in Windows Server environments. Here’s how to create and configure a GPO:
- Open the Group Policy Management Console (GPMC):
- On the Windows Server, open the Server Manager, then navigate to Tools > Group Policy Management.
- Create a New GPO:
- In the GPMC, right-click on the Group Policy Objects node and select New.
- Give your GPO a meaningful name and click OK.
- Edit the GPO:
- Right-click on the newly created GPO and choose Edit to open the Group Policy Management Editor.
- Under Computer Configuration or User Configuration, expand the settings you wish to configure (e.g., Policies > Administrative Templates).
- Link the GPO:
- After configuring the GPO, link it to a site, domain, or organizational unit (OU) by right-clicking the Organizational Unit or Domain and selecting Link an Existing GPO.
- Enforce the GPO:
- You can also enforce a GPO, ensuring that it takes precedence over others and is always applied.
- Test and Verify:
- After configuring and linking the GPO, verify that the settings are applied by running the gpresult command on client machines or checking the Resultant Set of Policy (RSoP).
Best Practices for Using GPOs
While GPOs are an incredibly powerful tool for system administrators, they need to be used thoughtfully to avoid misconfigurations or unintended consequences. Here are some best practices for using GPOs effectively:
- Keep GPOs Organized:
- Always name GPOs in a meaningful way to reflect the purpose of the policy. This will make it easier for you and your team to manage GPOs over time.
- Limit Scope and Inheritance:
- Apply GPOs only where necessary. Use the Security Filtering feature to target specific users or computers, and avoid applying policies at higher levels when possible.
- Use GPO Modelling:
- Use the Group Policy Modeling tool in GPMC to simulate how a GPO will apply in different scenarios, helping you avoid conflicts and unexpected behavior.
- Test Before Deployment:
- Always test your GPOs in a controlled environment before deploying them across the network to prevent errors from affecting a large number of systems.
- Regularly Review and Update GPOs:
- Regularly review your GPOs to ensure they are still needed and functioning as expected. As your environment evolves, GPOs may need to be updated to meet new requirements.
- Monitor GPO Changes:
- Use Group Policy auditing and logging to monitor changes to GPOs. This can help identify misconfigurations or unauthorized changes.
Common Use Cases for GPOs
GPOs are widely used to control a variety of settings across the network. Here are some common use cases:
- Security Policies:
- Enforce password complexity, lockout policies, and encryption settings.
- Software Deployment:
- Automatically install or remove software applications across the network.
- User Restrictions:
- Prevent users from accessing specific applications, modifying system settings, or using external drives.
- System Configuration:
- Configure settings such as Windows Updates, network drives, and printer mapping.
- User Profiles:
- Control user desktop settings, application preferences, and roaming profiles for a consistent experience across machines.
Troubleshooting GPOs
If a GPO is not being applied as expected, several troubleshooting steps can help resolve the issue:
- Check GPO Links: Ensure that the GPO is properly linked to the correct Organizational Unit or domain.
- Verify Permissions: Ensure that the appropriate security filtering is applied and that users/computers have the necessary permissions to apply the policy.
- Use gpresult: Run the gpresult command to see which policies are applied to a user or computer.
- Check Replication: In a multi-domain controller environment, ensure that GPOs are replicated properly across all domain controllers.
Conclusion
Group Policy Objects are an essential tool for managing Windows environments, offering centralized control over user and computer configurations. By understanding how GPOs work, their components, and how to create and manage them, administrators can ensure that systems are secure, compliant, and configured correctly. By following best practices and troubleshooting techniques, you can make the most of GPOs and streamline the management of your networked systems.
With the right GPO strategy in place, organizations can achieve consistent, secure, and efficient IT environments.
For a detailed, step-by-step installation guide, check out my video where I explain each step in detail. If you’re still facing any issues, feel free to leave a comment below, and I’ll be happy to help you resolve them.
Don’t forget to check out the YouTube video for practical demonstrations Watch the Video Tutorial Here